“There has been a 67 percent increase in overall spam volume and a 500 percent increase in image spam since Aug. 2006.”
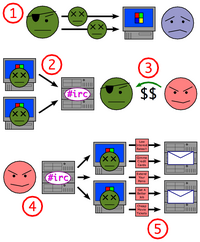 Illuminating (but seriously depressing) series of articles at eWEEK on botnets — arrays of 0wnz0r3d Windows computers assembled under the control of sophisticated “bot herders,” silently pumping every orifice of the interweb full of spam in all its forms. The virus that makes a machine part of a botnet does not cause harm to its host – like all successful viruses, it wants to assure its own survival. Amazingly, the latest generation of botnet software even installs antivirus software (a pirated copy of Kaspersky Anti-Virus, to be specific) to eradicate competing malware, so it can have the full resources of the infected host to itself.
Illuminating (but seriously depressing) series of articles at eWEEK on botnets — arrays of 0wnz0r3d Windows computers assembled under the control of sophisticated “bot herders,” silently pumping every orifice of the interweb full of spam in all its forms. The virus that makes a machine part of a botnet does not cause harm to its host – like all successful viruses, it wants to assure its own survival. Amazingly, the latest generation of botnet software even installs antivirus software (a pirated copy of Kaspersky Anti-Virus, to be specific) to eradicate competing malware, so it can have the full resources of the infected host to itself.
For a while, it looked like botnet activity was shrinking, but lately it’s seen a huge uptick. vnunet reports that a million-bot botnet is quietly being assembled around the world, and that we’ll soon see an even more massive onslaught of phishing and spam attacks.
The sophistication of these systems is amazing — the botnets even come with their own self-contained DNS system. “This allows a bot herder to dynamically change IP addresses without changing a DNS record or the hosting—and constant moving around—of phishing Web sites on bot computers.”
So can’t botnet hunters just focus on nailing the central command and control machines? Nope – that’s the “beauty” of using a peer-to-peer model:
Control is still maintained by a central server, but in case the control server is shut down, the spammer can update the rest of the peers with the location of a new control server, as long as he/she controls at least one peer.
One of the many factors that makes fighting back so hard is that infected bots expect incoming commands to be digitally signed. Commands from the bot herders to members of the botnet are securely encrypted, and virtually impossible to decipher or reverse-engineer.
The sophistication of modern spammers is impressive on so many levels. Image spam (e.g. Viagra ads that appear as graphics rather than text) has been especially vexing lately, as it seems to elude all filters. Since almost all anti-spam mechanisms — even collaborative ones like Akismet — rely to some extent on the ability to deduce unique “signatures” from a message, every single image sent by machines on a botnet has slightly different dimensions and characteristics, making it nearly impossible to nail down. I’ve even noticed random graphical noise splattered in the background of image spam lately – which prevents any two images from producing identical signatures.
I think I was wrong when I said recently that my IP firewalling script was becoming less effective because spammers had learned to spoof IPs. I believe now that the problem is that the botnets are so widely distributed that the same IPs don’t come up with enough repetition to be useful. Rather than spam spewing from a volcano somewhere in the Ukraine for a few days, it’s now more like a steady mist that suffuses the atmosphere – an endless acid rain emanating from everywhere at once.
What amazes me is that articles like this never seem to point out the obvious: The botnets are comprised entirely of Windows machines. There are currently approximately 5.7 million infected Windows computers out there, ready and able to join a botnet at any time. If I were the sysadmin of a Windows network, this would be significant information to me. It’s not that OS X or Linux are theoretically incapable of this kind of takeover, but the plain reality is that it doesn’t happen. And yet, articles like this never make a recommendation that admins consider a platform shift. Why?
Sadly, experts are starting to feel hopeless about their prospects of staying in front of the game.
We’ve known about [the threat from] botnets for a few years, but we’re only now figuring out how they really work, and I’m afraid we might be two to three years behind in terms of response mechanisms,” said Marcus Sachs, a deputy director in the Computer Science Laboratory of SRI International, in Arlington, Va.
Amazon is having serious issues with spam, as is del.icio.us. Of course one would expect large services to be constantly hammered with spam, but if the largest and best-funded commercial entities on the web can’t keep spam off their public doorsteps, you know things are getting serious out there.
It’s becoming increasingly popular for admins to block entire nations, either at the apache or at the firewall level. I’ve been tempted to do the same myself, but haven’t. Yet.
All of this applies to the interactive aspect of the web as much as it does to email. I deal with it on wikis, discussion boards, blogs, and apache logs (referrer spam). In recent months, I’ve seen them stuffing personal contact forms, and even the public jobs database at the j-school (which is absurd, since no job ever gets published without human review, but that doesn’t stop them from trying). Amidst all the Web 2.0 talk of participatory journalism, the wisdom of crowds, the read/write web, and two-way communication, it’s those very features that are being exploited by spammers and the massive botnets.
I worry that the openness that made the internet possible will ultimately become the sword upon which it impales itself. I see a future where everything is so locked down that all of the fun participatory stuff becomes impossibly difficult. I worry that someday email will only be feasible with whitelisting, that registration with identity verification will be required for all participatory web features, and that the concept of anonymity will ultimately become untenable.
Compare the atmosphere of the internet to the ecology of the earth. It took us millions of years to get to industrial civilization, then just a few decades to pollute our environment to the brink of sustainability. I worry that the internet is following a similar course – 30 years to become mainstream and five years to become so polluted it’s unusable.
Thanks Mal

The only real way to shut down these botnets is for a Malicious Virus to be released. It needs to only infect insecure Windows Machines (Easy), get past the BotNet AV software (hard), Propigate before releasing it’s payload, and has to completely disable the Network stack to all traffic on all ports (easy).
Of course, even if the Payload is something malign like Demolishing the network stack, but leaving User Data intact, it would still be highly Illegal and in America, the distributer would be charged with Terrorism, since they are restricting the trade of Capitalist Businesses (Spammers) on a Public (Socialist) network.
I don’t think migrating from Windows is a practical solution. The stats show that about 6% of the infected machines are Windows 98 and ME. So one in 20 of these infected computers is running a 6 to 8 year old OS. You can’t force people to upgrade. It’s not a matter of getting enough sysadmins to push their shop to Linux or Macs.
Half the infected machines are not even getting current security patches. The flip side of that is a frightening stat too, but the reality is that the unpatched, unmaintained older systems are at least half of the problem.
I’m inclined to think that we’re looking to the wrong places for solutions and police. Microsoft can’t help us. They’ve only just begun to make serious efforts to track and eradicate trojans. The ISPs, backbone networks and routers are probably where we need to be looking to choke the large botnets.
As one person I know commented, one of the largest cable networks doesn’t do an effective job of addressing the infections coming from their network.
I tend to think that one problem is the networks don’t want to assume liability by attempting to solve the problem and then being seen as responsible for failing to prevent infections.
The other problem is that the service providers seem to be lacking the competency and technical understanding to even attempt to control this. And the few who are able to study this kind of thing are like scientists observing and trying to interpolate a big picture from the little bits they can actually see.
I think the ISPs need to accept more responsibility and accountability for letting they customers get hijacked, and that perhaps aggressive filtering is needed to help plug the holes.
I spent much of the last half decade doing ISP support and watched the virus infections and trojans grow. I spent countless hours walking college students and little old ladies through scanning systems, and even arguing with IT students to try to convince them they were infected.
Eventually I just started aggressively plugging the abused ports on our routers. This had minimal impact on quality of service and left a lot of infected computers inside our network but helped prevent new infections spreading and complaints from upstream providers.
I’s a different and much more complex world now, and the sophistication clearly comes from people who are making enough money at this that they can afford to hire and attract the kind of talented programmers to exploit anything. These guys probably make more than the naive children in Redmond trying to plug the dyke with a finger.
So lets look to the folks who built the networks and infrastructure for ways to detect and isolate this kind of crap. Throw some money at Cisco and get the networks more active in caring about the abuse. Figure out how to isolate the bots at a network level, spam at the servers and clients, and eduction users and support staff better. The solution is as complicated and elusive as the source of the problem, but clearly what everyone is doing now is not working.
The real solution is to cut off the money supply TO the spammers. IE, make spam illegal, and fine the company being advertised. Second, it might help to make operating systems companies liable for damages due to their software insecurity.
-Jim
> Image spam (e.g. Viagra ads that appear as graphics rather than text) has been especially vexing lately, as it seems to elude all filters.
“Seems to” is it. [See link]
> I worry that someday email will only be feasible with whitelisting,
Given the prevalence of Internet Explorer (BTW, still not adequately secured by default in version 7), today the Web is only feasible with whitelisting.
> It’s becoming increasingly popular for admins to block entire nations, either at the apache or at the firewall level. I’ve been tempted to do the same myself, but haven’t. Yet.
If all you ever see is spam, hacking attempts, or other malicious traffic from a given IP range associated with a country, oh well . . .
Daniel wrote:
> The only real way to shut down these botnets is for a Malicious Virus to be released.
“Great minds,” and so forth . . .
> even if the Payload is something malign like Demolishing the network stack, but leaving User Data intact, it would still be highly Illegal
“You may as well be hanged for a sheep as for a lamb” is one of the reasons why IMO no-one not having a money-profit-making interest will write such a beast.
This made me think of A Rant About Usenet again.
And the problem with black/whitelisting are the false positives. My workplace blacklisted any access to heise.de (a well-respected German technical news publisher) because Heise also offers a number of pages executing known browser exploits.
That this is offered as a service so that Heise users can check their systems for unpatched holes failed to register with the security people in charge.
Mal – So half the machines on the botnets ARE relatively recent versions of Windows. Perhaps patched, perhaps not. But even when admins attempt to keep Windows machines up to date with patches, there’s such an endless succession of security issues and zero-day exploits that it’s almost impossible to stay out in front of it. With Windows, updates never seem to mean you have a reasonable expectation of security. For us at the J-School, the constant issues with Windows were reason enough to switch the entire school off of that platform (not to mention wanting a better experience in general for all users). What still puzzzles me is that our move to ditch Windows for Mac is so rare. I see admins all over the world sticking with Windows “no matter what” when they could just make all of these problems go away and take their platform to an entirely new level.
I totally agree about putting responsibility for this kind of activity in the hands of ISPs and network providers. I wonder what it would take to make that happen. Network ownership can be so fuzzy and people don’t like to take responsibility for parts of the network outside their direct control. Meanwhile the spammers are working under the “bits don’t stop at the border” model.
And as you discovered, trying to work on this directly with customers just doesn’t scale – the profit of a single customer in a year is eaten up by 30 minutes of phone support. Assuming the user even cares to begin with.
Mark – interesting technique on the Thunderbird content filtering, though it would seem to mark quite a few false positives (and the comments say as much).
Lars, that Usenet rant was a good read, thanks.
Plz abuse this botntes’ server. plz plz plz
213.239.219.153:1863
209.250.234.164:6798
216.12.205.178:5555
72.36.171.250:5051
88.198.36.87:5050
88.84.144.181:9050
88.84.148.49:1122
194.116.209.105:5555
200.251.187.2:4212
193.138.222.11:9999
66.252.31.210:9501
88.84.152.230:7766
134.197.89.1:8782
80.97.51.143:7777
211.115.112.76:6270
89.163.182.20:3921
66.252.31.210:9501
66.109.25.116:11640
208.53.143.101:2329
tcteam.ath.cx:2006
dv.tetovalive.de:9501
gt.albashow.de:8350
xp.i-am-leet.com:8202
suzi-love.ath.cx:2006
h3x.tetovalive.de:5051
207.81.157.91:8822